Archive
All Posts
-
-
-
Scaling databases
You would hear a lot about the three V’s of data - Volume, Variety & Velocity. Every enterprise and almost any application of enterprise grade is facing growth in consumption and therefore, growth in the data it consumes, generates, processes & stores as well as the forms of the data thats been processed.
-
Going NoSQL
NoSQL database offer great power to developers and organizations in form of fluidity of data definition and data structure. However like any other transition, moving from relational databases to NoSQL also requires a mindset shift and if you do not stop thinking relational, you may land in more problems than the one you are trying to solve by using NoSQL. This post tries to provide some pointers to catalyze such transition.
-
Microservices Design Anti-patterns
With the emergance of cloud and cloud-native technologies, Microservices Architecture has surfaced as the default architecture for custom applications including enterprise as well as web applications. One of the keys to realizing microservices architecture is Domain Driven Design to identify microservices for your application domain.
While there are plenty of content out there providing guidance as to how to break down your domain into sub-domains and identify your microservices, I try to touch upon a couple of anti-patterns often observed during domain driven design.
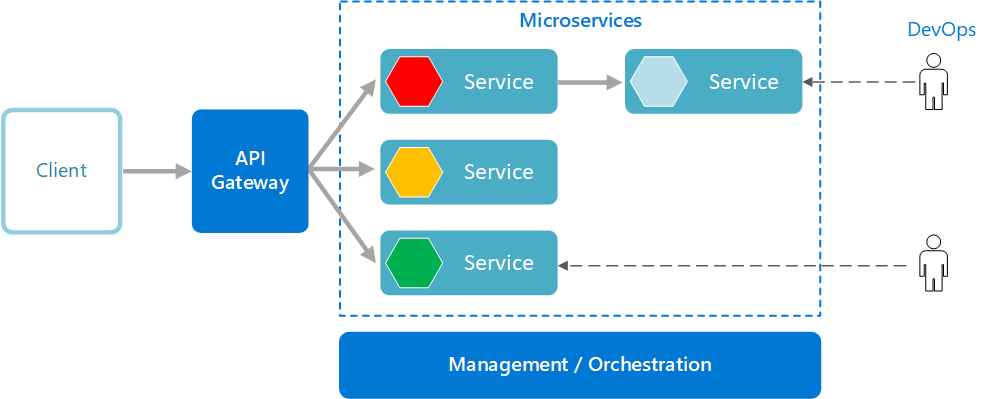 Source - Microsoft Azure documentation
Source - Microsoft Azure documentationLayering microservices
The idea of microservices was to move away from layered architecture to a mesh where the logical component structures have evolved to accomodate fluidity and flexibility. However, I have still observed quite a few teams adapting microservices trying to find microservices for each layer. This stems from the old habits of separating concerns - especially the responsibility of presentation, business logic and entity model.
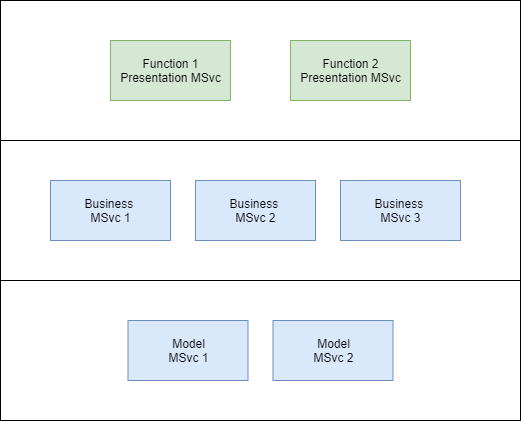
The core principle of microservices architecture is to separate concerns by sub-domains and functions instead of whether the piece of code relates to dealing with data or dealing with logic. More often than not, you cannot separate the understanding of the data and the business logic and have different developers code that; microservices scales the application domain down to a level where a developer can and should write both the aspects of the application anyways. You could still choose to separate source files that do data operations and that execute business logic within the microservice code.
The reason this isn’t a good idea is because it introduces unnecessary network communication between the microservices therefore impacting performance and resilience of the features.
Business Entity driven microservices
In domain-driven design approach, though its recommended to identify and use domain entities to identify microservices in a sub domain however, attempting to build a “single enterprise-wide entity model” and using that to drive microservices identification is an anti-pattern. Its common enough to have a name for itself - Anemic Domain Model.
It stems from the fact that when translating business processes and business entity model to application architecture, we often overlay the business processes across the business entities i.e. treat business entities as swimlanes in a cross-functional flow diagram format. This automatically leads to entity-bound function mapping.
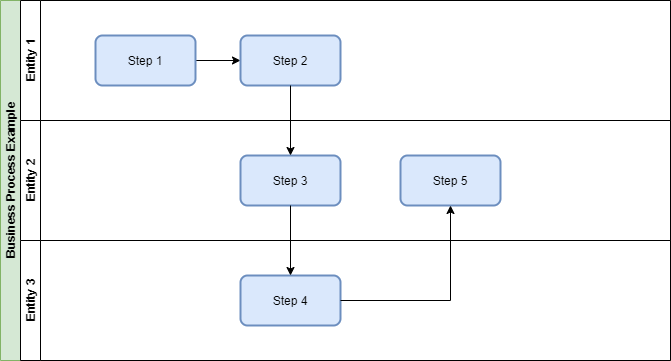
On the contrary, domain-driven design breaks down domain into sub-domains and attempts to identify and form microservices for the sub-domain with their relevant view of the closely related business entities. This is called bounded context based design approach which creates business function focused boundaries between microservices and also minimize the impact of a change – in terms of number of microservices requiring a change for a new feature etc. Of course, you can still have adapter and BFF microservices where source-specific protocol or data transformation and user journey specific API are needed however, consuming all these as layers should not be the thumb rule but a need based approach only.
Deployment model
Last of all, the funniest of observation is about how microservices are deployed in various organizations. In spite of decent aware of the “One microservice per process; one process per container (or VM)” thumb rule, I come across instances with multiple processes in a container image far too many times for my liking. This is typically driven by the need to share external infrastructure resources e.g. storage volumes. The trade off is surely the ability to scale and operate the microservices independently as well as the ability to isolate faults.
I welcome comments on these anti-patterns and inputs for any more patterns being observed that I can explore and add to this or a later post.
-
Hosting a Website or Blog on Github pages
Festive holidays usually offer me an opportunity to execute some personal projects. This past Diwali weekend allowed me one such opportunity and I grabbed it to migrate my blog to Github Pages. This does pose a limitation of largely being able to host a static website only however, it serves the purpose of a blog quite well and most of the dynamic functions on a personal website or blog can be met easily with 3rd party service web integration.
-
Standardized Cloud Management
With multiple cloud platforms with their individual management interfaces – both web and CLI, it is getting harder to keep with the capability & features of each of the services they provide, even to keep up with the range of services offered in the first place. While 3-4 major cloud platforms are surfacing as industry leaders, there are others in the game as well thus, adding to the sheer amount of it. Its all the more important as more and more enterprises are moving to hybrid cloud solutions consuming more than 1 of these platforms to host their applications. There are enough drivers for going hybrid cloud too – avoid vendor lock-in, leverage best-in-class from wherever its available etc.
-
Basic Analysis of Farm Bills
Having read some bits of the 3 farm bills and thinking about it, I have more concerns with it than the benefits I see and in my humble opinion, the leadership of the farm protesters may not be focusing on the right bits by seeking MSP guarantee included in the two relevant bills. Here is a brief summary of my thoughts, comments are welcome -
-
Idealog: How does your family know what you own?
This is a conceptual app which allows an individual to store information about his/her assets, investments & insurances in a way that its secure while you are around and its provided to the family in the event of.
-
Idealog: Responding to pandemic situations
Have you noticed how so many celebrities and other Mumbai residents have been posting their electricity bills on social media generated by Adani complaining how high it is? Its clearly a case of missing readings because they aren’t able to send meter readers out therefore generating bills based on estimates.
-
Idealog: Remote Spectator Reaction Broadcast System
With COVID19 still around, sports events have not been happening and even when they start, they will need to start with empty stands. The players will miss the audience in the stands rooting for them and encouraging them. For Indian teams, it means missing the noise. Here’s a solution
A system which allows all TV spectators of the events to turn on audio capturing on their phone or smart device which they watch the match at home. Each spectator participating gets assigned to a stand in the stadium – reflecting his/her virtual seating in that stand. The system then intelligently combines the audio tracks of all the people and collective sound tracks or noise tracks are formed for each of the stands in the stadium where different fans are assigned to different stands. The sound system of the stadium is utilized to broadcast the combined noises of the spectators in the stadium in a distributed manner. There can be higher allocation to home team fans compared to the visiting team to ensure the home team advantage is retained.
-
COVID19 India Growth Analysis
Started this article as a periodic report and my analysis of COVID-19 in India. I chose to focus on the rate of growth with daily resolution deeming it to a key indicator of progression and control; having observed the trends of some of the countries which are closer to recovery. Daily growth rate is nothing but new cases being reported in relation to the existing number of cases.
-
Effective web performance testing
There are quite a few reasons for teams to entirely circumvent performance test in a web project however, the two biggest reasons for such organization behavior are Lack of skilled performance engineers & performance testers and Lack of robust understanding of performance test results of an application therefore project teams faced with numerous questions around it.
-
Idealog: Meeting action tracker
How about a service which captures the actions out of a meeting in your stead.
-
2 ways in Gmail to find out who’s spamming you
In spite of all the spam filters and intelligence that email service providers have built over time, so much spam still lands in your Inbox. Ever wonder who’s letting your email address land in the hands of the spammers?
-
Internet Firsts
Cleaning email archives over the weekend, came across emails from my first email account on usa.net in 2000 – the first time I got access to internet (though I had access to a PC since 1993 I believe – MS DOS, no HDD). Took me back to exploring my firsts on internet and here is list of what I can recall –
-
Idealog: Peer to peer cash transactions
I’ve been thinking how simple and wonderful will it be if I can open up an app, specify the amount I wish to withdraw and find depositors with similar amounts around me, connect with them, collect my cash, transfer the money to their bank accounts and we’re done. And of course the other way round.
-
10 reasons you should learn story telling
Irrespective of the profession you are in, one thing you need to do on a daily basis is communicate. That’s true even if you are sorting mails for postal service or writing software pieces from the privacy of your room or operating a train engine. There’s shouldn’t be any big deal about communication since that’s what separates us from the rest of the animal kingdom – the multi-layered sophisticated and rich methods of communication we’ve established. We write, we speak, we sing, we dance, we do body language, gestures, facial expressions, non-facial expressions and to beat it all, some of us have gotten around to establishing a language in the freaking silence. But, it is and we also have miscommunication, misunderstanding and misinformation happening all around us.
-
How to use RTFTemplate to generate report documents
If you are looking at generating document report based on templates, RTFTemplate is a good choice. It allows you to use from a list of template engines at the back and allows for good user experience for template creation as well as the final product.
-
Idealog: Indoor positioning system
GPS and GLONASS are satellite based positioning systems which work wonderfully outdoors however, due to wall penetration issues, indoors is a different story. This is a problem if you are trying to get to a place in a huge Railway station, Airport or a mall. Briefly, positioning with GPS works is as follows –
-
External scripts & their impact on page performance
Any modern website or mobile site heavily relies on scripting to make its pages more interactive and neat to provide an overall good user experience. All these scripts are usually included as external scripts in the page. Not only this, 3rd party external scripts are also included for a bunch of purposes including marketing, click tracking, web analytics, social integration and the like. Where these bring considerable value to the table however, the value generated can very well be offset by the drop in traffic or transactions if user experience is damaged by poor page performance. And hence, this post.To begin with, let’s understand the seven key factors which impact page response time –
-
Word processing Java utility
A while ago, I ran into a word processing requirement of converting documents to web pages and processing the document text to extract information. While working on this, I ended up wrapped a few APIs e.g. JODConverter into a small set of utility classes. I am not sure of the value of to a developer however, documenting this might just help someone reach the open source APIs I used and use this as sample code. So, here I go with some of the use cases –
-
Idealog: Health Buddy
Here’s a thought.
-
Idealog: Public transport navigation
While thinking about how public transport can be encouraged in a city like Gurgaon and in a metropolitan like New Delhi, which essentially has three states running public transport services. One of the things I find missing is that beyond Delhi Metro, no other public transport system has its information digitally available.
-
FAQ: How do I get myname.com website up?
From people in IT and outside, this is definitely the most frequent question I get asked in different forms. So, here I go…
-
Jersey on WebSphere issue
I was just starting creating Jersey RESTful services on WebSphere 8.5 and came across an error.
-
How to double agricultural production in 5 years
-
Infosys 3.0 followup
Two years ago, I mentioned Infosys’s intention of getting of services strategy to become a wholesom technology organization. Here’s the link.
Apparantly, it didnt work out too well for them as this article on The Next Web very well describes how our (Indian IT) current ways of working – though worked wonderfully well in services and outsourcing, might not enable us to make this shift just yet. -
Any how fast is your ISP?
-
Installing Drupal on your EC2 Instance
Going on with the Hockey site, http://www.seventyminutes.com is now an Under Construction site. Starting with Drupal….
I am sure a lot of people have been through this and might find this fundamental however, coming from a non-php background, I found this a little annoying at first.
When I started with my EC2 instance yesterday, getting started with Apache and MySQL was piece of cake. And then came Drupal… forgive my ignorance, I did everything Drupal Installation guide asked me to do except installing PHP. Ohh yes… missed that one.
Just when I opened my first php page in the browser I realized, I need PHP. Here I go with yum again however, it didn’t go until I noticed that instead of package php.x86_64 which kept throwing error messages of conflicts with some version of httpd modules, I would need to install php54.x86_64 and that worked.
Restarted Apache and I was at the install guide of Drupal.. a step ahead now, however not too later, I was looking at a Verify Requirement screen calling out 3 PHP modules missing. Tried searching for them on yum and installing them. No go. Didn’t even see the 54 version of these modules.. until I used search all and got them all.
UPDATE
Did I mentioned, you’d see MySQL in the database type list only if you’ve installed the MySQL php extension (again with a 54 suffix).
If any of you face an issue with “Array to String conversion” notice messages during the later stages of installation and subsequently on all your web pages, this link has a fix
http://stackoverflow.com/questions/17904933/notice-message-array-to-string-conversion-in-menu-router-build-while-installi
Very well then… a step ahead now… keep you posted !!! -
Chrome Bookmarks Bar Line spacing
If you use bookmarks bar to any extent in Chrome, you’d surely have noticed how the padding / line spacing between bookmarks has blown up. Personally, its fairly irritating for bookmark folders where scroll starts to appear for 20 odd list.
Here’s how to fix it –
</p>- Close Chrome
- Go to your Chrome shortcut properties by
- Right clicking Chrome shortcut on your desktop or
- Shift + Right clicking Chrome pinned to task bar or
- Right clicking Chrome shortcut in the Programs menu
- Append “ –disable-new-menu-style” to the Target text
- Apply & Close
- Open Chrome
Voilà !!!
Update :
I had this working for over 3 weeks and suddenly it didn’t work anymore. Back to the blown up bookmarks again. I typically use the Pinned shortcuts as would most users. Started Chrome from the Program menu and its working again from Programs menu as well as the task bar shortcut. Seems like some kinda command caching in Windows. Need to figure out more.</div> -
Cloud Housing
With the rise of cloud computing and shared technology infrastructure, it’s not far away that we’d start seeing other industries introducing cloud offering.
Looking at the current trend in real estate in India, cloud is already underway. Just look at the way real estate commercial investment has been shaping up. However, the only real consumption example is perhaps the resort memberships. Looking at the real estate prices in cities like Gurgaon, we might soon see Cloud Housing. It’s like a township or a housing society where everyone’s a tenant and builder is the owner or perhaps a group of investors who got it built from a builder.
Since, there is no capital investments from consumers, every amenity is an add-on fee and management is centralized… it’s a perfect setup for a typical middle class who cannot surely afford a house with today’s prices. The only hindrance would be the Indian mindset of living in an owned house. However, as the cloud computing has been adapted by corporates moving from a mind set of IT infrastructure assets and data security, its quite possible for a home-owner to become a cloud-home-owner as well.
See where it goes… -
How to achieve geo-distributed site
Why do I need a Geo-distributed site?
If you are serving to a global audience (or even an audience across geographies), it is very desirable to have your site geo-distributed to enable you to serve your site to users from closer to their location. So, instead of a site being hosted in a set of servers in one location, you host a set of servers in a set of locations which are geographically distant and strategically chosen to be closer to the biggest user clusters’ locations.
Typically, these are known as mirrors. Mirrors are used by all global sites, especially all sites enabling file transfers/downloads. In fact, these sites let you choose your mirror for download to rule out any error while automatically selecting a mirror for you when you first visit. -
Next on Cloud
What could be the next cloud offerings?</p>
Basic idea of cloud is to reduce cost by sharing resources. So far, infrastructure (IaaS), server-side software (Paas, SaaS) have already been adapted. Perhaps, next we are going to see software licenses available on shared basis.
Come to think of it, it might shape the future software licensing very differently. -
Websphere Portal Server – some hacks
We recently worked on making URL’s of a WCM driven site SEO friendly. It has a couple of problems – the home page URL itself was not just the domain name but also had a trail of wps/wcm/connect/whatnot after it which was common for all the pages of the site as well.
How we resolved this was using reverse proxy @ the web server to hide the common part of the URL. We subsequently ran into a couple of new issues.
1. Generated links on pages were not relative
We had to re-write URL’s using regular expressions in all the responses. We had created a bunch of proxy context for a lot of our site libraries. We had to handle them all in the re-writing
2. What to do about already ranked pages with old URL’s
Since, we had used proxy, the old URL’s still worked. We didn’t use redirects as we were not sure how that could impact our page ranks. Setting canonical URL’s to the newer URL’s did the trick for us. Hence, page was accessible through both the URL’s for a while however, the search engine URL’s started reflecting the new URL’s within days.
Here is a list of a few reference articles and discussions which we came across and were helpful.
Setting Page specific title
Clean and SEO friendly URL’s
SEO friendly URL – 2
Some more on SEO friendly URL’s -
Infosys 3.0
Read about Infosys starting a software products startup.
What thrills me most about this is the fact that eventually they realized how important, though risky, it is to have something which can bring in recurring income.
Hopefully, this would bring the culture of products in IT in India and hopefully, some big ones beyond business solutions.. may be a middleware or a big time Operating System someday. -
Dont steal data casually !!!
Its pretty common amongst Indian IT professionals to take out pieces of code or data they find valuable and take it away; something they consider their “owned” brainchild which it isnt..
-
P vs NP solved – or is it?
Just read a news item about a American scientist of Indian origin has submitted a paper on solving P vs NP. Here’s the link
-
J2EE: Too many open files
Now this thing is eating my head since yesterday, and I have done all i could to stop it from coming up again on my server.
The issue is with Checkpoint production server where the following error keeps popping up twice a day and the server is literally held up till you restart it –
May 18, 2010 3:03:34 PM org.apache.tomcat.util.net.PoolTcpEndpoint acceptSocket
SEVERE: Endpoint ServerSocket[addr=0.0.0.0/0.0.0.0,port=0,localport=19638]
ignored exception: java.net.SocketException: Too many open filesjava.net.SocketException: Too many open files
at java.net.PlainSocketImpl.socketAccept(Native Method)
at java.net.PlainSocketImpl.accept(PlainSocketImpl.java:384)
at java.net.ServerSocket.implAccept(ServerSocket.java:453)
Having Googled enough, we reviewed all the jars for reloading itself through out the application, reviewed the whole code for closing all File streams blah blah blah. Nothing worked.
Finally, working on getting all the open files in a shell file passing a process id to lsof, found a properties file open a bunch of time. On checking further, realized the ResourceBundle was an instance variable in a frequently used utility class. Changed to static variable, problem solved. The unix/linux commands required to check the no. of open files that can be opened by a user are typically in ulimit and the hard limit can be checked by
ulimit -aH -
JSP 2.0 – Quote not escaped
Encountered a weird problem today, a running application on Linux/Tomcat 5.5 starting crashing at various places after re deployment without much code issues.
Issue came up in all the JSP pages which had request.getParameter call within value attribute of any tag. Logs showed the following JasperException
Attribute value request.getParameter(“XXX”) is quoted with ” which must be escaped when used within the value
Simple fix, append the following to JAVA_OPTS variable in catalina.sh
-Dorg.apache.jasper.compiler.Parser.STRICT_QUOTE_ESCAPING=false
Works !!! -
Conserve Energy – tips
Its good to see energy conservation catching up with people a bit these days. Its something which is comfortably resisted in routine life of a middle class Indian like me. I personally face a lot resistence in my house with everyone finding me nagging on petty things like leave a tap dripping or a light on in the stairway etc. I keep naggin ’em anyway. Here are a few tips you could probably use to make your contribution to energy conservation.
-
Introduction to Hacking - Javascript Injections and Social Engineering
One of the very commonly used techniques for hacking, when it comes to web sites, is Javascript injections. Javascript Injections are a technique in which, using javascript, we change the content of a page without having to navigate away from it or saving it offline. The most popular example you would find online would be of altering the admin email address which is stored in a hidden field in the page.
-
Hacking History - A popular basic virus
I know I will be disappointing a lot of people who might have been looking forward to learning How to hack into a network ? or How to crack a software ? or How to break into a popular website ? I assure all those that its not exactly what you would find here. However, the stuff you would find here would be definitely be a lot more fun and relevant to achieving something that can be way beyond stupid things like these. Keep the faith.
-
Random Thoughts
-
Introduction to Hacking Funda – Beyond Technology
disclaimer – None of the stuff in this blog or in the leading series is meant to be used for any illicit purposes and is meant to grow technically and ethically and contribute to the technical community and help do our job better.
-
Introduction to Hacking – SQL Injections
Disclaimer – All the post of this series are meant to discuss the basics behind the art of hacking and not to provide exploits, irrespective of the fact whether I am aware of any or not. Assure you that the stuff provided is surely more than sufficient for any intelligent person to come up with a good hack.
-
Technical Helpdesk
Ok… the funniest of the things happened last evening. We are currently in a process of integrating a renouned Payment Gateway with our site and they have provided an API for it. We have been having compatibility issues of their API with our IBM JRE being used in our project.
-
Intro to hacking – Essentials
* Just couldnt sleep thinking that I might be leaving a few souls disappointed with my previous post, so just had to write this one.</p>
</span>
A hacker is anyone who has to skills of a hacker and understands the spirit. Skills of a hacker include the following, in my opinion –
- Atleast one programming language or scripting language.
- Knowledge of HTML and Javascript.
- Basic database skills and PL/SQL.
- Basics of Operating System and networks.
- Very good troubleshooting skills and logical thinking.
- Ability to quick-read and understand code patterns.
- Social Engineering
Some of these things are neccessary, however, traits like troubleshooting and recognizing code patterns is something one can learn over a period. Anything beyond this would make it easier for the guy to accomplish whatever he wants to just by providing more options. Knowing atleast one high level programming language thoroughly and one scripting language is a real must as is knowledge of Operating systems and HTML.
Just to give you a small example of how things work while hacking and you can use one of these skills to accomplish a task. Imagine a website which required a password to get through, which of course you dont have. There are multiple ways to find out the password – ask the site admin(dont laugh guys, its A way and is really an option) OR find out the way authentication would be done by the site and figure out a way to crack it. In a hypothetical situation, suppose the site admin has server side scripting to authenticate his password from some encrypted source to which you have no access to, however, there is a forget password button which sends an email to the site admin with the password in it. Now, in most of the static sites, there is not backend database to store info so most of the information is stored within the web content, either in files other than the pages being served or in the pages as hidden fields which can easily be looked up by viewing source for a web page.
In such a case, we use Java Script Injections. Java Script injections is a technique by which using the browser’s address bar, we issue java script commands to the browser to dynamically change values of the web page form including the ones which are hidden or read only. So, you know what to do.
Now, this teaches us a few important lessons as a hacker and as a developer –
- All hacks are in some way exploiting a loophole left by one of the developers or admins.
- There is a lot of logical thinking involved in trying to figure out what all are the possible hacks that could be used for a certain target. And of course, common sense.
- Address bar of Internet Explorer is a powerful tool.
- Its not a good idea to leave important information in any form in the HTML at all.
Think the hacking way, understand the hacking spirit and you would develop application that would defy security threats.
🙂 If you thought you just learnt a big trick on how to get into a site without authenticate, you are mistaken. This isnt something that would work on most of the sites you land on. It would take a lot more thinking and application than this to use Java Script injection to really accomplish anything at all.
-
Significance of Server Resource configuration
First a question, if your web application or portal are not performing as you expect it to, what would be the first thing to target ? In most of the cases, the action would be to review and optimize the database queries, looking for memory leaks and ensuring resource cleanup. One thing that normally comes last into mind is the resource configuration parameters and other server configurations. How often do you see a server configuration and resource parameters altered from their default values while setting up a server for production environment? Besides only a few organizations, especially in banking and financial domains, most of the organizations dont pay enough attention to this aspect.
-
Learning Vs Learning
When I was growing up (I still am..) there were a lot things that used to bother me in school. There was absolutely nothing I would take or learn without being absolutely sure of it. They even went on to say that I’m from Venus coz when I was 14, I insisted how everything that WE had learnt was required for life on a planet existing on Venus inspite of which there was no life (known to us) on the planet, which according to me meant either of the two –
-
Where are India\'s Newtons and Einsteins
Proud as I am of the APJ Abdul Kalam, Ashok Jhunjhunwala, Homi Bhaba, JC Bose, Vikram Sarabhai and a few others, however, I still feel that we have not produced as many innovators as we could have considering the average IQ of Indians and the rich knowledgebase that we carry (especially in medical science).
-
The Indian Kid who rocked! or did he
I faintly remember a news from last year (or the previous) when there was this Indian teen who built an Operating System claimed to be a step ahead of Windows that time and one of the Indian IT companies (HCL I guess) came forward to take up the detailed study, and promotion thereon, of that OS. It became an instant news, exciting everyone in the industry and witnessed lots of people from the community and the media going all out praising for the innovative minds of Indian genius. And the news died its death, as did the OS I guess. I tried to google on the subject and found the following link http://hindustan.net/discus/messages/60/13420.html
-
Domain Names and Brands - Lack of understanding
I got atleast 10 people showing me the site http://www.airtel.com/ and laughing off how Vodafone has taken over Airtel site…. and I pity everyone who’s thinking something like this without understanding what actually is behind all this.
First the domain name airtel.com doesnt belong to Bharti Tele Ventures Ltd, the Airtel service provider that we know in India. They have their site up at http://www.airtel.in/ or at http://www.airtelworld.com/</p> -
A show for the Gypsys
I happened to visit a music show in the city for the Gypsyies. There is an organization called NOW (Nomads of the World) which organized a music workshop over the last week for world peace. The important thing though, was the participants which included some nomads from Rajesthan, school kids from the city and a composer from Italy whose first name is Andrea (coz I dont remember his full name 🙂 ).
Now, the schools kids composed, during the workshop, a song on world peace which they performed with an amazing zeal and passion which can be seen only at that age of innocence. This was followed by a series of Jugalbandi between the Italian composer and the Rajesthani nomads which was kicked off by Andrea singing the Gayatri Mantra. The jugalbandi was not always enticing, however, what was fantastic to see was, the people who didnt even have a verbal communication channel and used a translater at all times off the stage, had an amazing chemistry on stage during the performance and how they took to each other’s culture with such respect. I dont think the Italian understood what the lyrics of the song sung by nomads for Meera really meant but he sung it with the same passion as the nomads did and the same stood true for Andrea’s compositions being performed in tandom with the nomads. The special part was to see chemistry between Andrea and Rakesh, an 8 year old nomad who rose to the occasion and never lost control of his instrument during the dance steps that he never looked like stopping. He was just in a zone where he just couldnt see or hear anyone but for the music he was so lost in. Both the people never had to share a word, but change in the tempo or scale in one’s performance would immediately reflect in other’s right after an eye contact. It was so amazing to see.
Truly one of the best and most teaching experiences of my whole life. -
Basic Java Tips and Tricks
Following are just a few tips and tricks around java technologies – -
National Growth
Onus of National Growth
